Manufacturing the worst hit by ransomware in India: Palo Alto Networks’ Unit 42 research
Palo Alto Networks’ Unit 42 recently
released the Ransomware Retrospective 2024: Unit 42 Leak Site Analysis and Incident Response report 2024.
As part of the Ransomware Retrospective, they studied 3,998 leak site posts
from various ransomware groups. Leak sites are platforms where threat actors
publicly disclose stolen data as a means of coercing victims into paying
ransom.
Key findings from this investigation:
Unit 42 saw a 49% YoY increase in multi-extortion ransomware attacks from 2022
- 2023 globally. In India, the manufacturing sector has been the most targeted
industry for ransomware extortion in 2023. Of the 3,998 leak site posts from
2023 globally, LockBit ransomware remains the most active, with 928
organizations accounting for 23% of the total. LockBit is also the most active
group in APAC and India (note: this was before the recent law enforcement
disruption of LockBit). At least 25 new ransomware leak sites were observed in
2023; of which Akira led the way.
Anil Valluri, MD and VP, India and
SAARC, Palo Alto Networks, said, "In India, the Manufacturing
sector has emerged as the primary target for ransomware attacks over the past
year. This unsettling trend underscores the critical vulnerabilities within the
Indian manufacturing sector, where limited visibility into operational
technology (OT) systems, inadequate network monitoring, and suboptimal
cyber-hygiene implementation have left organizations exposed. Organizations
must implement enterprise-wide Zero Trust network architecture to create layers
of security that limit an attacker from successfully moving laterally around
the network.â€
“In a rapidly transforming country
like India, organizations are constantly grappling with a blend of modern and
legacy systems, creating huge cybersecurity gaps. And with attackers
increasingly targeting software and API vulnerabilities, our findings come as
no surprise. Thus, organizations need to move away from point-solutions that
increase time to detect/respond and end up being more costly in the long-term.
Fully integrated cybersecurity solutions will also do away with the idea of
vendor sprawl, an issue that CISOs shouldn’t concern themselves with during
times of duress.â€
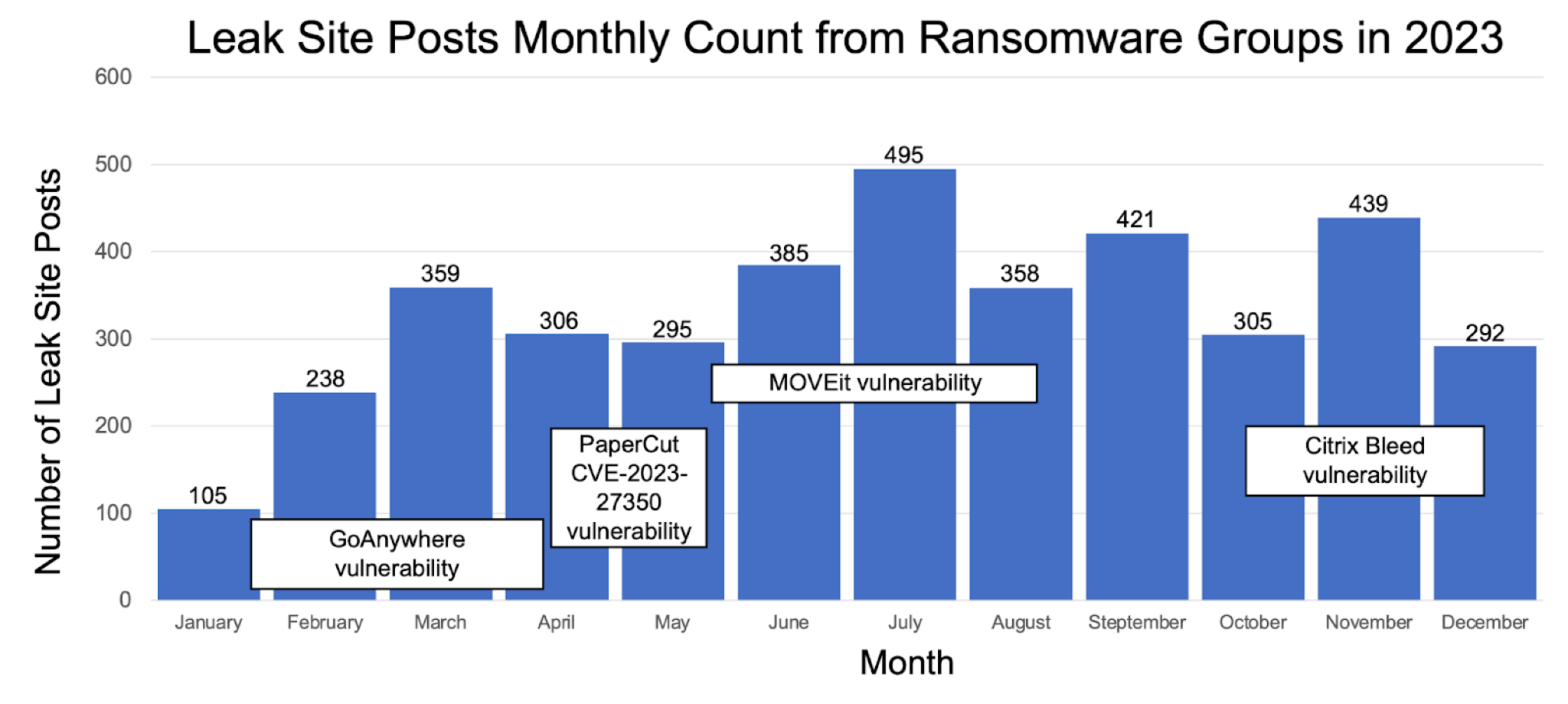
The 3,998 posts from ransomware leak
sites represented a 49% increase compared to 2022, where 2,679 posts were
observed globally. This increase can be attributed to zero-day exploits
targeting vulnerabilities for MOVEit Transfer SQL Injection and GoAnywhere MFT,
among others.
As further evidence, when reviewing
the number of compromises reported by ransomware leak sites, sporadic spikes
were observed (see figure below). These loosely aligned with periods where
ransomware groups began exploiting specific vulnerabilities.
Unit 42 2024 Incident Response Report: Speed of Exfiltration +
Vulnerabilities Driving Activity
Unit 42 analyzed more than 600
incidents from 250 organizations for the 2024 Unit 42 Incident Response
Report. This investigation went beyond ransomware leaksite posts
into the overall casework volume. While phishing has historically been a
popular tactic with attackers, the report found that it is declining, but only
sort of.
From a one-third share of initial
access incidents in 2022, phishing has dropped to just 17% in 2023. This
indicates a potential de-prioritization of phishing as cybercriminals adapt to
more technologically advanced – and perhaps more efficient – infiltration
methods. More advanced threat actors are moving away from traditional and
interactive phishing campaigns to less noticeable and possibly automated
methods of exploiting system weaknesses and pre-existing credential leaks.
Other key findings from the report include:
â— More-Sophisticated
Threat Actors Are Gaining Initial Access Differently: There has been a
discernible rise in the exploitation of software and API vulnerabilities.
Exploiting such vulnerabilities accounted for 38.60% of the initial access
points in 2023, up from 28.20% in 2022.
· Threat Actors Grab
Data Indiscriminately: In 93% of incidents, threat actors took data
indiscriminately rather than searching for specific data. This is up from 2022,
when 81% of cases involved non-targeted data theft. In 2021, it was even lower
at 67%. The surge points to a growing trend among cybercriminals who seem to be
casting a wider net, gathering any data they can access rather than expending
effort to locate and extract particular datasets.
· Extortion tactics
to maximize yields: Interestingly, while the rate of harassment and
other extortion tactics w.r.t. Ransomware has remained steady over the past few
years, the rate of harassment in cases where payments were made has
jumped by 27x since 2021.
· Higher demands,
lower payouts: In 2023, median ransom demands
increased from $650,000 to $695,000 (3%↑) but median payouts decreased from
$350,000 to $237,500 (32%↓). This can be potentially attributed to
organizations calling-in Incident Response teams with negotiation capabilities
(which fewer did in the past).
Huzefa Motiwala, Director, Systems
Engineering, India and SAARC, said “While the surge in ransomware
incidents is concerning, there are glimmers of hope amidst the challenges. The
data reveals a promising shift in organizations' response strategies, with a
notable increase in median ransom demands countered by a decrease in median
payouts. Since organizations are more willing to call-in Incident Response
teams, threat actors are happy to take the path of least resistance. Which, in
most scenarios, is to grab what they can get, and move on.â€

























Leave A Comment